Curious about Actual Fortinet Certified Solution Specialist (NSE7_ZTA-7.2) Exam Questions?
Here are sample Fortinet NSE 7 - Zero Trust Access 7.2 (NSE7_ZTA-7.2) Exam questions from real exam. You can get more Fortinet Certified Solution Specialist (NSE7_ZTA-7.2) Exam premium practice questions at TestInsights.
With the increase in loT devices, which two challenges do enterprises face? (Choose two.)
Correct : C, D
With the increase in IoT devices, enterprises face many challenges in securing and managing their network and data. Two of the most significant challenges are:
Start a Discussions
exhibit.
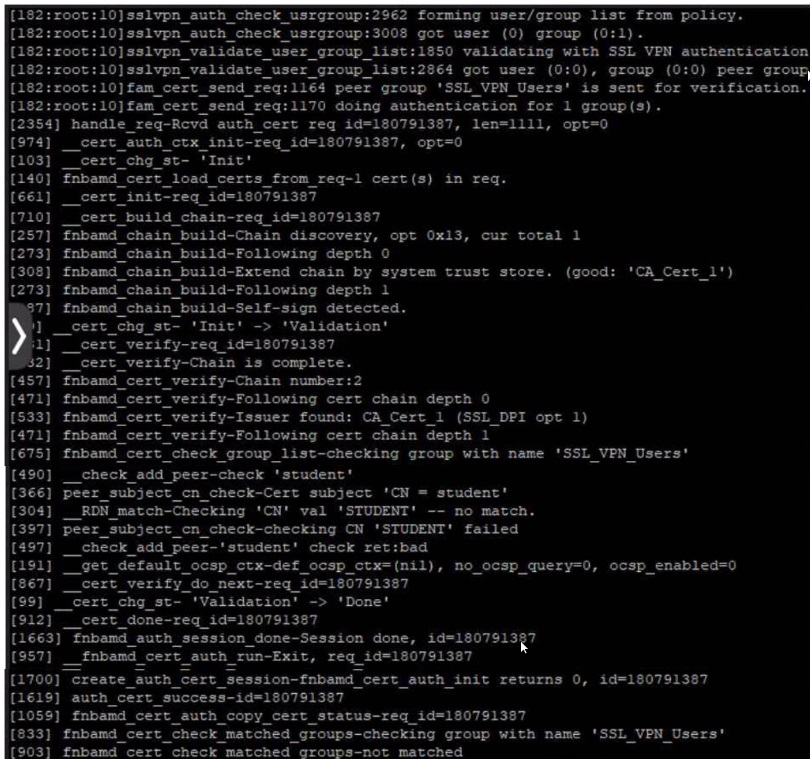
User student is not able to log in to SSL VPN
Given the output showing a real-time debug: which statement describes the login failure?
Correct : C
Given the output showing a real-time debug, the statement that describes the login failure is:
C) student is not part of the usergroup SSL_VPN_Users: The debug log contains a line that says 'fnbam_cert_check_group_list-checking group with name 'SSL_VPN_Users'' followed by 'peer_check_add_peer_check_student' and later 'RDN_match-Checking 'CN' val 'STUDENT' -- no match.' This suggests that the certificate presented has a common name (CN) of 'student', which does not match or is not authorized under the 'SSL_VPN_Users' group expected for successful authentication.
Start a Discussions
In which FortiNAC configuration stage do you define endpoint compliance?
Correct : C
Start a Discussions
Which three statements are true about a persistent agent? (Choose three.)
Correct : B, C, E
A persistent agent is an application that works on Windows, macOS, or Linux hosts to identify them to FortiNAC Manager and scan them for compliance with an endpoint compliance policy. A persistent agent can support advanced custom scans and software inventory, apply supplicant configuration to a host, and be used for automatic registration and authentication.Reference:=
Start a Discussions
Which three statements are true about zero-trust telemetry compliance1? (Choose three.)
Correct : A, B, D
In the context of zero-trust telemetry compliance, the three true statements are:
A) FortiClient EMS creates dynamic policies using ZTNA tags: FortiClient EMS utilizes ZTNA (Zero Trust Network Access) tags to create dynamic policies based on the telemetry it receives from endpoints.
B) FortiClient checks the endpoint using the ZTNA tags provided by FortiClient EMS: FortiClient on the endpoint uses the ZTNA tags from FortiClient EMS to determine compliance with the specified security policies.
D) FortiOS provides network access to the endpoint based on the zero-trust tagging rules: FortiOS, the operating system running on FortiGate devices, uses the zero-trust tagging rules to make decisions on network access for endpoints.
The other options are not accurate in this context:
C) ZTNA tags are configured in FortiClient, based on criteria such as certificates and the logged-in domain: ZTNA tags are typically configured and managed in FortiClient EMS, not directly in FortiClient.
E) FortiClient EMS sends the endpoint information received through FortiClient Telemetry to FortiOS: While FortiClient EMS does process telemetry data, the direct sending of endpoint information to FortiOS is not typically described in this manner.
Zero Trust Telemetry in Fortinet Solutions.
FortiClient EMS and FortiOS Integration for ZTNA.
Start a Discussions
Total 30 questions